I wrote earlier in the week about Randy Hefner’s article that characterized the present state of SOA security as “good enough and getting better”. If you design your security architecture well, you can iterate on it and implement more sophisticated security models as you need them. This is something I agree with completely–in fact, this is the guiding principle behind how we build the SecureSpan Gateway product line here at Layer 7. But I’m a vendor; of course I’m going to say that. Instead, let me prove it using some real examples.
Suppose we have a simple warehouse application we want to make available to our field staff. The application resides deep inside our corporate network, and our field staff need to use the public Internet to access it. The good news is that this application publishes a service composed of four simple operations:
Warehouse Service
-
listProduct()
-
getProductDetails()
-
placeOrder()
-
currentOrders()
This will make it easy to build clients that can access it. The bad news is that it has no security protecting it in any way, as it’s been assumed to be in a secure environment.
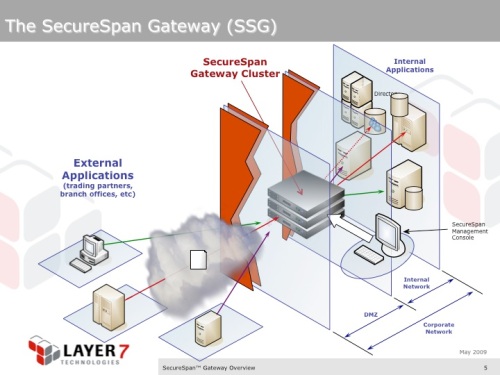
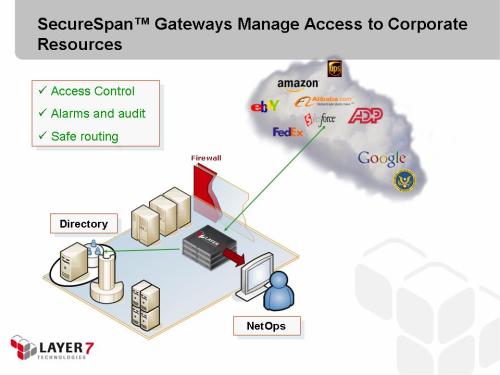
We’ll use a SecureSpan Gateway in front of the application to be the secure “front door” to these services. The Gateway will provide policy-based security, that can be easily administered by a dedicated security professional–not the developers who wrote the original warehouse app. This is what Randy and Forrester recommend as a best practice. Here’s how it looks:
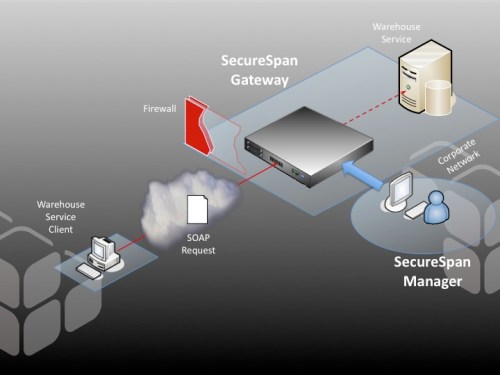
A simple, edge-of-network deployment of a SecureSpan Gateway as a border guard for internal services.
Scenario #1: Simple SSL
Randy suggested that given the right architecture, you can begin with a simple security model and evolve it. That’s what I’ll do here. I’ll begin with a very simple, uniform security policy governing access to the service:
Policy #1
- Incoming connection must use SSL
- Send the request content to the internal warehouse service.
I’ll admit that this isn’t much of a security model–it has no authentication, authorization, or audit. But it does illustrate how you can layer on some simple policy to the internal service: here, by only accepting connections that are using SSL. Thus, we’ve put a constraint on the system that between the external client and the SecureSpan Gateway we must have confidentiality and integrity.
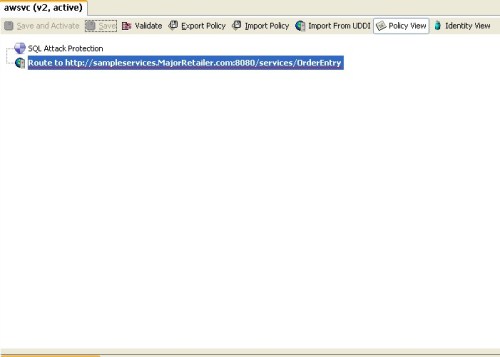
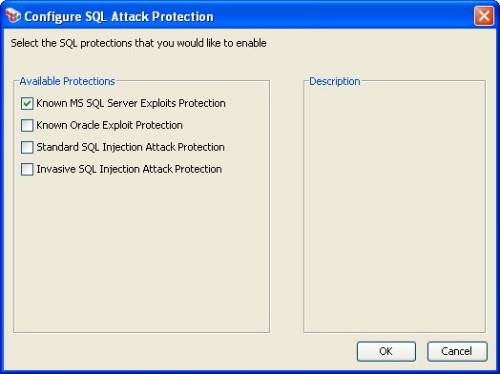
Policies are created in the SecureSpan Manager, which is the administration console for single gateways or clusters (a logical grouping of gateways that shares policies and critical state info and is administered as a whole). The SecureSpan Manager has a useful wizard that allows you to compose basic security policies using only the WSDL description of a service as input. I won’t demonstrate it here, but instead skip to the wizard output, which is an executable policy:

This policy will be executed automatically whenever the Gateway receives a message destined for the warehouse service. It’s composed of just two assertions that implement the policy requirements we listed above. In SecureSpan, assertions are strung together into algorithms that describe how the gateway should process a stream of XML content. SecureSpan ships about 100 standard assertions. These can be used to do everything from authentication, transformation, SLAs, routing to different transports, audit, logical flow control, orchestration, etc. There’s also a pluggable model for building your own custom assertions, which you can use to solve those unusual problems that can’t be overcome with basic components. It’s a lot like the shell scripting philosophy in Unix: give people a kit of basic sharp tools and there’s no limit to what they can build.
Scenario #2: Add Client-side Certificate Authentication and Authorization
Suppose we want to add client authentication to the policy. There are dozens of different authentication modes in the Web services standards, and a number of informal ones we see regularily in the field. We support virtually all of these. In this example, let’s use client-side certificates, and let’s add an authorization component to only permit people in the sales group to access the warehouse service:
Policy #2:
- Incoming connection must use SSL
- Client must be challenged for a certificate, and this certificate must be valid, and be issued by an authority we trust
- Client must be in the sales group, as defined in the gateway internal identity provider
- Send the request content to the internal warehouse service (as before).
Think about what you would have to accomplish to implement this on the application server you host your services on. Now think about getting this consistent across a farm of servers. Finally, consider how you would maintain this consistently across different systems, like Microsoft .NET and WebSphere. It’s a big challenge. In contrast, here’s what it looks like in SecureSpan:
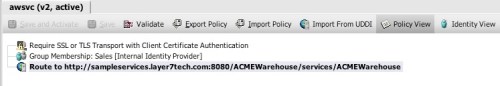
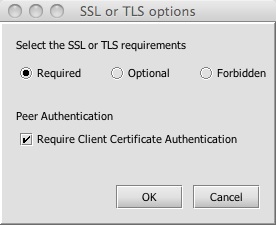
Notice the first assertion now declares that it will challenge the client to authenticate itself using the client-side certificate authentication protocol built into SSL. This is configured by adjusting the assertion details, which are accessible by double-clicking the assertion:
I’ve added a new assertion that adds authorization (or entitlements) by imposing group membership requirements. I simply dragged it in from our palette and dropped it into the policy. Here, I’m leveraging group definitions that were defined using our internal identity provider. This is a localized directory shared across SecureSpan Gateway clusters. Administrators create identities here, define groupings, and issue certificates using the Gateway’s integrated Certificate Authority (CA) capability. These features are convenient because they allows you to work with identity-centric policies without being forced to call out to an external LDAP, Identity and Access Management (IAM) system, or PKI authority. (Of course, if you want to go external, we have connectors into, well, pretty much all of them.) The internal identity provider is very useful for testing or development–and demonstrations like this where we are trying to keep things simple.
Scenario #3: OASIS Web Services Security WS-S Message-based Security
Now let’s make a really radical change to our security model. We’ll move from transport-level, SSL security to a more sophisticated message-based security model. This supports different transports–such as going over a JMS Message-Oriented Middleware (MOM) provider like MQSeries, or transfer of XML content as a file over FTP. It can handle asynchronous, and non point-to-point messaging, which are difficult or impossible to achieve using connection-based SSL. Here’s the new policy:
Policy #3:
- Authenticate identity using the OASIS WS-Security Kerberos Token Profile
- Ensure that the message contains valid, digitally signed time stamps. These could be used to add uniqueness in the message as a means to defeat replay attacks (there are various other strategies to achieve this as well).
- If the operation requested is placeOrder(), decrypt the order contents elements in the message using the AES-192 cipher, a symmetric key encryption mechanism. Do this in compliance with the OASIS WS-Security standard.
- Regardless of the operation, ensure that there is a valid signature spanning the body of the message to ensure that nothing was altered in transit. This also establishes a binding between the content and the identity we validated in step #1.
- Client must be in the sales group, as defined in the internal identity provider (as before).
- Send the request content to the internal warehouse service (as before).
Our security model is becoming fairly complex, and it’s important to note that it is by no means complete. We haven’t even begun to address how the response from the service should be handled (right now it’s just relayed unaltered from the service); however to keep things simple in the example we’ll confine ourselves to this, knowing that it is incomplete.
Here’s what this policy looks like in the SecureSpan Manager. Note that it’s simple to read and understand, which is important when designing security implementations. Complexity increases the chances of errors going undetected:
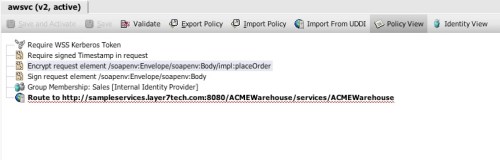
To write this I simply deleted the SSL assertion and dragged in four new ones. To configure the encryption on a particular element, I opened the detail pane of the encrypt request element assertion:
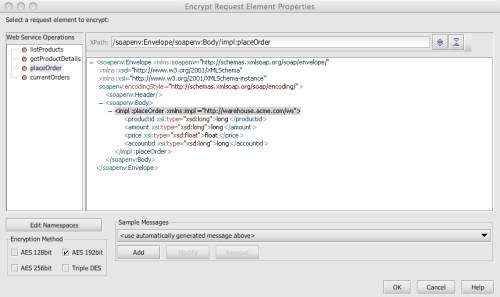
This pane reflects on the schema bound to the original WSDL that describe the warehouse service. It allows me to just point at the elements I expect to find encrypted (or signed). The gateway takes care of the heavy lifting of XML decryption at run time using our acceleration technology. This panel provides a standard message stereotype to work with, or I can load a sample message to describe an even more realistic scenario.
The time spent converting from SSL-based security model to the much more sophisticated WS-Security policy was all of about 30 seconds. So what we’ve done here is shown how you can start simple, and grow your security model over time with very little effort or risk.
Simple SOA Security
When I was young my Dad was tough on tools. I quite clearly remember him stating “if your tools don’t work for you, get different tools”. This was usually followed by the offending tool being tossed into the garbage because it didn’t serve its intended purpose. A better one–one that solved the problem it was designed for–inevitably showed up soon after. Somehow, this has always stuck with me.
SOA tools need to work just as hard, and if they aren’t useful, they need to face a similar fate. SecureSpan Gateways need to offer flexibility, because the truth is, everyone has different integration challenges in the SOA world. But SecureSpan also needs to be simple enough to resist misconfiguration by virtue of the complexity of SOA security standards (more on this topic in a future post). These are actually two opposing forces, and it’s not trivial to find a useful balance between the two. SecureSpan has achieved that balance. When we do find case where it fails, our judgment is as unequivocal as my Dad’s around the chisels and wrenches in my his toolbox: replace it with something that works for you.