James Urquardt, from Cisco, published a review of the US Government’s recently announced cloud initiative. I had the pleasure of sharing a panel with James recently at GigaOm Structure, and his CNET column should be on your must-read list if clouds are of interest to you.
In this article, James makes an interesting point that the government is really following the “Adopt at your own pace mentality” with respect to cloud. Obviously this isn’t about moving IT completely into the cloud–let’s face it, governments, of all organizations, hold data that will always be inappropriate for public cloud deployment. But it does demonstrate that a perfectly reasonable strategy is to create the opportunity to move select applications into the cloud (such as blogs, as the article mentions), and provide a mechanism so that these can coexist with existing internal IT. This is the so-called hybrid approach (particularly if there is a private cloud as part of the “internal” deployment).
But hybrid clouds face a big problem. To be useful, there must be secure communications between internal applications and new services deployed in the public (or semi-public) cloud. Amazon recently announced it’s Virtual Private Cloud initiative to address this issue. I was encouraged by their efforts; clearly, Amazon is taking the hybrid model very seriously–no doubt they’ve had a lot of customers asking them to solve this problem. However, I do question the strategy of deploying a VPN tunnel between internal IT and a public cloud. Despite efforts to secure and make private the operating environment of the public cloud, the VPN solution remains a risky proposition.
The trouble with VPNs is that they are indiscriminate over traffic. The trust model of VPNs is based on both ends being equal secure. A VPN makes sense when you integrate a branch office into your central corporate network, as the later is subject to the same corporate security standards and policy. It can be dangerous if the remote site is one where you have any less control over the entire security model, as is the case in the cloud. Imbalance in security implementation is an opportunity for attack. If a single application on the cloud side is compromised, a system cracker can then leverage the VPN tunnel to get full access into the internal network. (This same problem exists with conventional VPNs and laptops, and believe me, it keeps security guys up at night.)
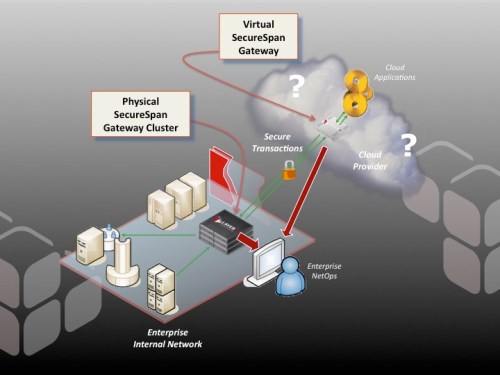
A better solution is to constrain communications on a service-by-service basis, managed under policy control. That way, if a system is compromised, it provides limited opportunity to launch a further attack. Here you are creating zones of trust between services, which is much more finely grained and deliberately constrained. The Layer 7 version of the secure hybrid model looks like this:
Here, virtual and physical SecureSpan appliances coordinate communications between internal applications and services residing in the cloud. All transactions are managed under policy control. They are rigorously monitored, scrubbed for threats, and constrained to the appropriate parties. Architectures like this allow organizations of any size to move at their own pace into the cloud. It’s a model we’ve been advocating for some time. SecureSpan is already the security foundation of what is arguably the largest private cloud in the world, which is an existing government initiative that predates this latest announcement.

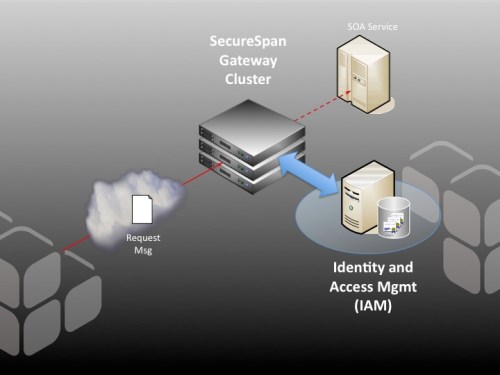 an investment in Identity and Access Management (IAM) infrastructure; however, this is not sufficient on its own for SOA access control. That’s where Layer 7 can help. Deployed in combination with an IAM system like OpenSSO, SecureSpan does the heavy lifting of XML processing and enforcement, but delegates the access control decision process (and often identity token validation) to the existing, familiar IAM infrastructure. It’s a powerful combination, and one that extends existing investment in IAM into the SOA world.
an investment in Identity and Access Management (IAM) infrastructure; however, this is not sufficient on its own for SOA access control. That’s where Layer 7 can help. Deployed in combination with an IAM system like OpenSSO, SecureSpan does the heavy lifting of XML processing and enforcement, but delegates the access control decision process (and often identity token validation) to the existing, familiar IAM infrastructure. It’s a powerful combination, and one that extends existing investment in IAM into the SOA world.